Privileged access protection at scale—without the vault
Enforce security the moment privileged access happens. Eliminate the need for slow vault rollouts, credential onboarding projects, and disruptive agent deployments with a vaultless PAM strategy.
Privileged access protection at scale—without the vault
Enforce security the moment privileged access happens. Eliminate the need for slow vault rollouts, credential onboarding projects, and disruptive agent deployments with a Vaultless PAM strategy.
Privilege is everywhere. PAM is not.
Security around privileged accounts still fails, even with a vault in place. Vault-based Privileged Access Management was built for compliance and password control, not to stop modern identity attacks. The result is poor posture and exposed privileged access that attackers exploit.
Why traditional PAM falls short
Narrow coverage
Protection is mostly limited to the crown jewels (Tier-0 accounts).
Low adoption
Onboarding is slow and resisted, so coverage never scales.
No runtime protection
Checked-out or valid credentials can still be misused.
High operational burden
Agents, password rotation, and integration projects delay value and protection.
Cost overruns and inefficiencies
Over-licensing and under-utilization lead to major cost overruns.
You don't need a vault to secure privileged identities.
Vaults serve compliance, not security. Instead of locking credentials in a vault, Silverfort takes a new approach. Vaultless PAM protects privileged access—human, machine and AI—at runtime with diverse controls that bring immediate value.
No complex deployment. No session disruption. No credential checkout.
Discover every privileged identity automatically
No more guesswork.
Enforce security when access happens
Prevent misuse before it starts.
Eliminate standing privilege with Just-in-Time access
Permanent admin access is an open invitation.
Prevent lateral movement and privilege escalation
Stop attackers even if they have valid credentials.
Secure service accounts without breaking anything
No identity is out of reach.
Right-size your PAM investment and reduce cost
Expand coverage quickly and efficiently.
Discover every privileged identity automatically
No more guesswork.
Enforce security when access happens
Prevent misuse before it starts.
Eliminate standing privilege with Just-in-Time access
Permanent admin access is an open invitation.
Prevent lateral movement and privilege escalation
Stop attackers even if they have valid credentials.
Secure service accounts without breaking anything
No identity is out of reach.
Right-size your PAM investment and reduce cost
Expand coverage quickly and efficiently.
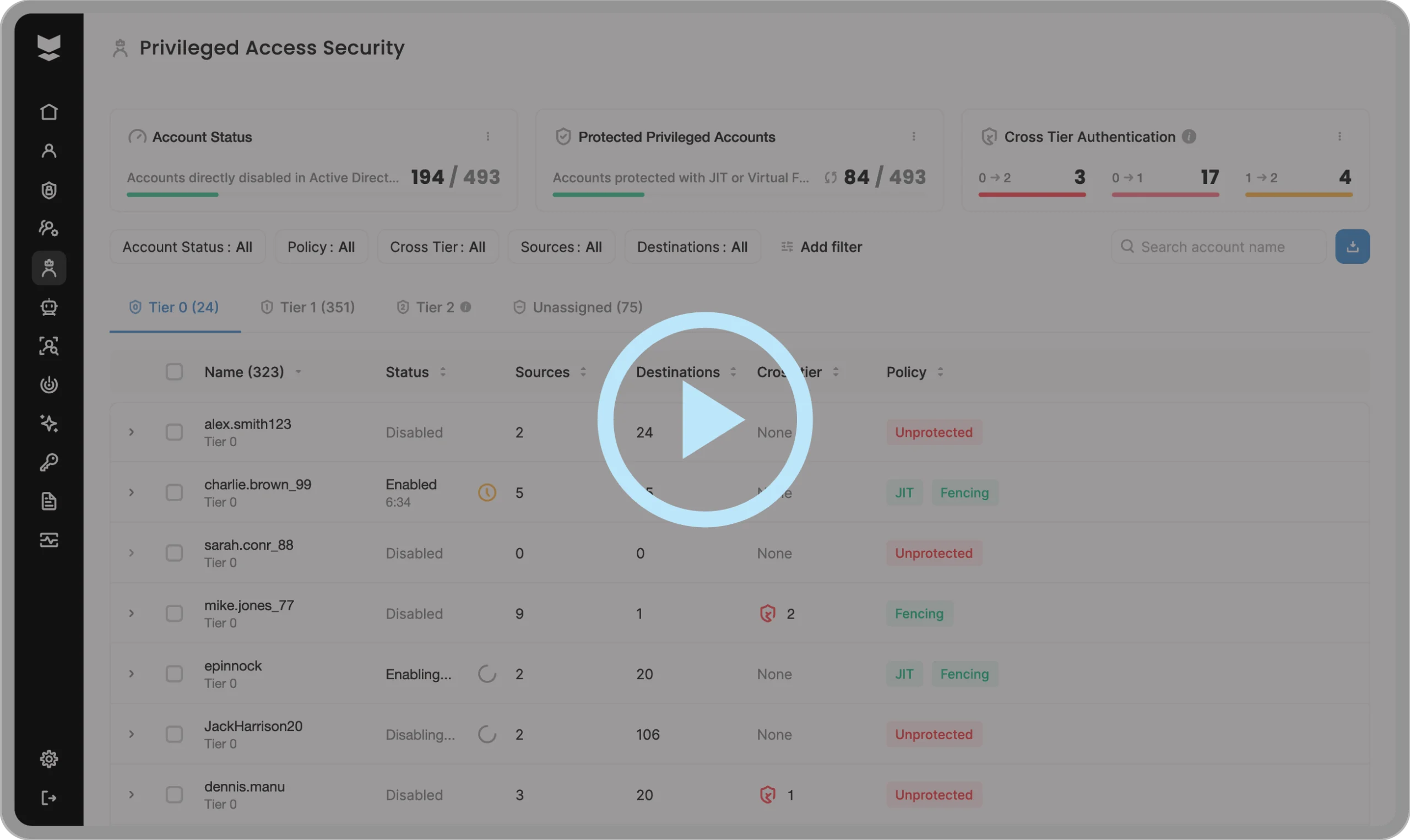
How Vaultless PAM works
Silverfort evaluates every privileged access request in real time and enforces policies before access is granted. If required, Silverfort triggers MFA, enforces Just-in-Time access, applies segmentation, or blocks the request. If approved, authentication proceeds normally with no workflow changes.
By leveraging the full Silverfort platform, you get scalable protection and measurable risk reduction across all identities:
Full visibility of all identities
Human, machine, and AI, across all environments.
MFA for admin tools
Enforce MFA on PowerShell, PsExec, WMI, RDP, SSH & other native tools.
Service account protection
Prevent unauthorized use with virtual fencing and usage policies.
Just-In-Time access
Eliminate standing privilege and grant access only when needed.
Authentication firewall to block risky access
Enforce tier segmentation at the point of authentication.
Actionable access intelligence
Analyze every authentication to uncover misuse & excess privileges.
Identity Threat Detection & Response
Detect & stop identity-based attacks in real time, before they escalate.
Identity Security Posture Management
Continuously identify and remediate identity exposures and hygiene gaps.
Built for any organization at any stage of your PAM journey
Whether your PAM program is mature, stalled, or never started, Silverfort delivers real security outcomes without operational drag. If you have already invested in a vault, we help you complete the journey while right-sizing investments. And if you haven’t, we help you skip the pain entirely.
With PAM: Rethink or extend your privileged access protection
Right-size your PAM to focus on Tier-0 and compliance, and use Silverfort to quickly scale protection to every other privileged account.
- Stop expanding complex onboarding projects.
- Freeze unnecessary license growth.
- Deliver protection at scale, quickly.
- Protect more. Spend smarter. Reduce real risk.
Without PAM: Get full privileged access protection from day one
Silverfort delivers PAM-level visibility and protection without vaults, agents, password rotation projects, or workflow disruption.
- Skip multi-year rollout and onboarding battles.
- Avoid operational friction.
- Get immediate privileged access protection.
- Scale security to every corner of your business.
Traditional PAM vs Vaultless PAM
Beyond the vault
Every privileged access secured, automatically and continuously.
Complete coverage
Human users, service accounts, and AI agents.
All tiers
Protection across every privileged level at scale.
No frictions or delays
Fast, simple, cost-effective rollout with high ROI.
Inline enforcement
Every privileged access request validated in real time.
Traditional PAM
Vaultless PAM
- Vault-based credential control
Runtime authentication enforcement
- Manual onboarding that takes months or years for a small subset of accounts
Automatically discover & protect all privileged identities at scale, in weeks
- Limited coverage, focused primarily on human admins
Protects all privileged identities at scale, both human and non-human, including service accounts
- Dependent on password rotation, creating operational burden and a false sense of security
Real-time access controls and policy enforcement that proactively reduce risk at the moment of authentication
- Complex deployment and workflow disruption
Seamless integration into existing environments, no workflow changes
- Expensive licenses with low utilization and limited ROI
Broad coverage, high utilization, measurable risk reduction
FAQs
We already bought a PAM solution. Why do we need this?
The real question is not ownership. It’s outcomes.
Most organizations have a vault but only protect a fraction of their privileged identities. Onboarding stalls. Service accounts remain exposed. Licenses go unused.
Silverfort closes those gaps. It scales protection beyond the vault, enforces controls at runtime, and delivers measurable risk reduction across all privileged access—fast.
This is not about replacing what works, but fixing what doesn’t scale.
Does Silverfort replace our existing PAM vault?
Not necessarily. It can, but it doesn’t have to.
Some customers replace their traditional PAM after struggling with slow deployment, limited coverage, and low adoption. They choose Silverfort as the new control plane for privileged access because it scales protection across all privileged identities without operational drag.
Others keep their vault for Tier-0 and compliance-driven use cases. In these environments, Silverfort extends protection across Tier-1, Tier-2, admin tools, and service accounts, while allowing customers to right-size unused licenses and reduce cost.
In both cases, the outcome is the same: broader coverage, faster protection, and measurable risk reduction.
If there’s no vault, how does Silverfort control privileged access?
Silverfort controls privileged access at authentication runtime.
Every privileged request is evaluated in real time using Silverfort’s patented Runtime Access Protection (RAP) technology. MFA, Just-in-Time access, segmentation policies, Least Privilege, virtual fencing, or access denial are enforced before access is granted. Protection happens inline, not through credential checkout workflows.
How is vaultless PAM different from password rotation?
Password rotation changes credentials periodically. It does not stop misuse of valid credentials between rotations.
Silverfort reduces risk when access is attempted by validating context, enforcing access controls and policies, blocking risky and cross-tier access, and containing lateral movement in real time.
Can you protect service accounts without breaking applications?
Yes. Silverfort applies virtual fencing policies to restrict where and how service accounts authenticate. Enforcement happens at the authentication layer, so systems continue operating normally, without the need for rotation and with no operational disruption.
How long does deployment take?
Deployment typically takes hours in smaller environments and days in large global enterprises. Customers gain visibility and start enforcing policies almost immediately.
Is this only for large enterprises?
No. Any organization with privileged accounts faces the same identity risk. Vaultless PAM scales across mid-market and global enterprises, across industries, and across hybrid or on-prem environments. The problem is universal, and the solution scales accordingly.