Secure the heart of enterprise authentication
Protect Active Directory. Prevent identity-based threats. Block misuse in real time. All without disrupting your business’ day-to-day.
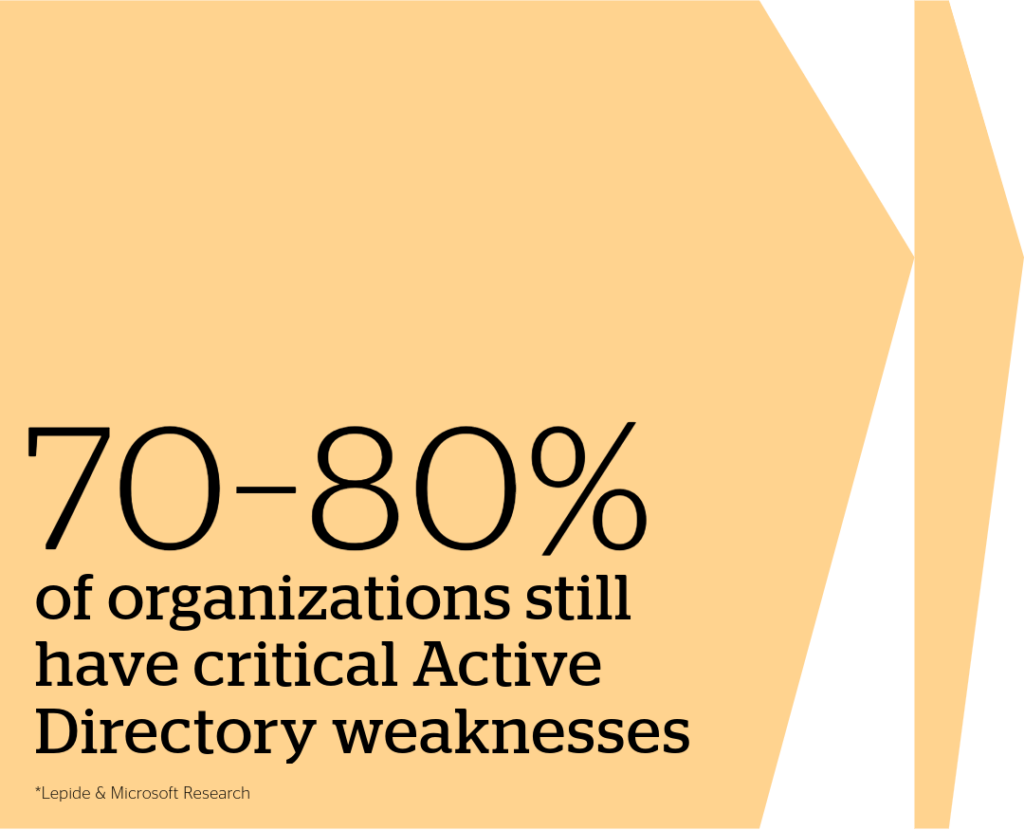
Active Directory wasn't build for modern threats
Active Directory (AD) is still the backbone of enterprise authentication, yet years of identity tech debt has created a sprawling attack surface.
Once AD is compromised, attackers own your environment through the same trust your business depends on.
- A compromised domain controller means total loss of control.
- MFA gaps and lack of visibility allow stealthy privilege escalation.
- Even small misconfigurations can cascade into enterprise-wide breaches.
Ebook
Active Directory Exposed
Protecting the cornerstone of enterprise identity
Get practical strategies to defend the identity infrastructure every attacker targets.
Ebook
Active Directory Exposed
Protecting the heart of enterprise identity
Get practical strategies to defend the identity infrastructure every attacker targets.
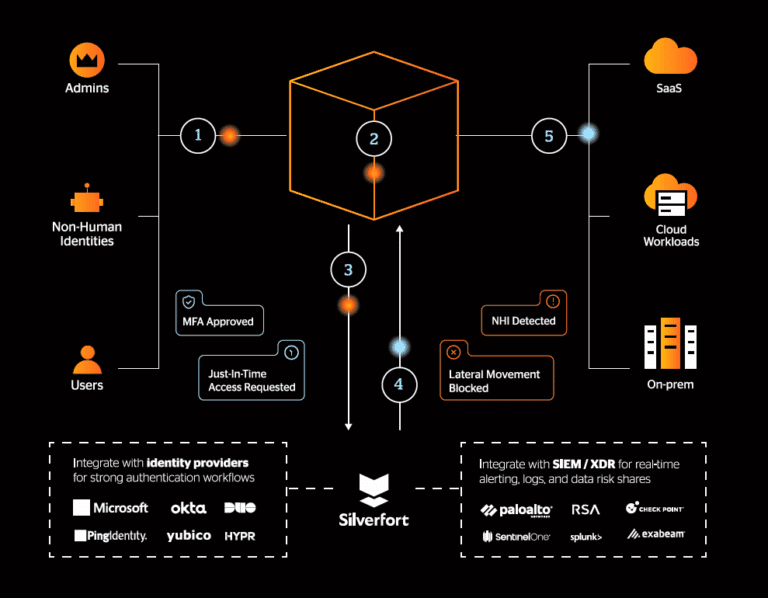
The Silverfort Identity Security Platform
The only platform built for runtime Active Directory protection
Unify visibility across every authentication
Strengthen Active Directory hygiene at scale
Enforce adaptive protection at runtime
Close MFA blind spots
Detect and stop identity attacks
Modernize without disruption
Unify visibility across every authentication
Strengthen Active Directory hygiene at scale
Enforce adaptive protection at runtime
Close MFA blind spots
Detect and stop identity attacks
Modernize without disruption
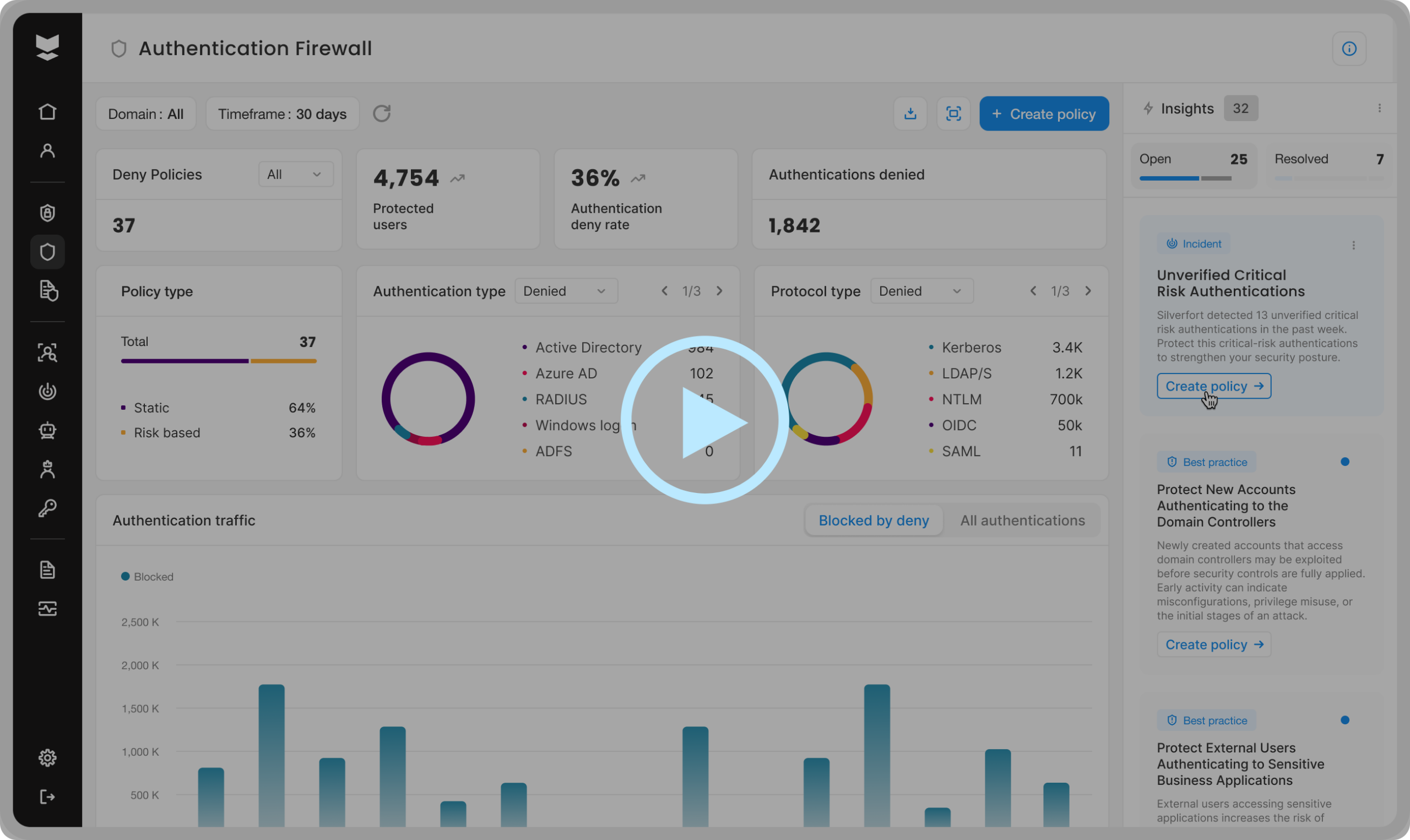
How it works
Verify every AD authentication across users, service accounts, and systems, and enforce protection in real time.
User requests access from IAM infrastructure
IAM infrastructure forwards request to Silverfort using our patented Runtime Access Protection (RAP) technology
Silverfort analyzes risk & triggers inline security controls if needed
Silverfort returns security verdict to IAM infrastructure
IAM infrastructure grants or denies access
Operating from within the IAM infrastructure, we see and protect every authentication—so you can finally have peace of mind.
Operating from within the IAM infrastructure, we see and protect every authentication—so you can finally have peace of mind.
Operating from within the IAM infrastructure, we see and protect every authentication—so you can finally have peace of mind.
Operating from within the IAM infrastructure, we see and protect every authentication—so you can finally have peace of mind.
Operating from within the IAM infrastructure, we see and protect every authentication—so you can finally have peace of mind.
User requests access from IAM infrastructure
IAM infrastructure forwards request to Silverfort using Runtime Access Protection (RAP) technology
Silverfort analyzes risk & triggers inline security controls if needed
Silverfort returns security verdict to IAM infrastructure
IAM infrastructure grants or denies access
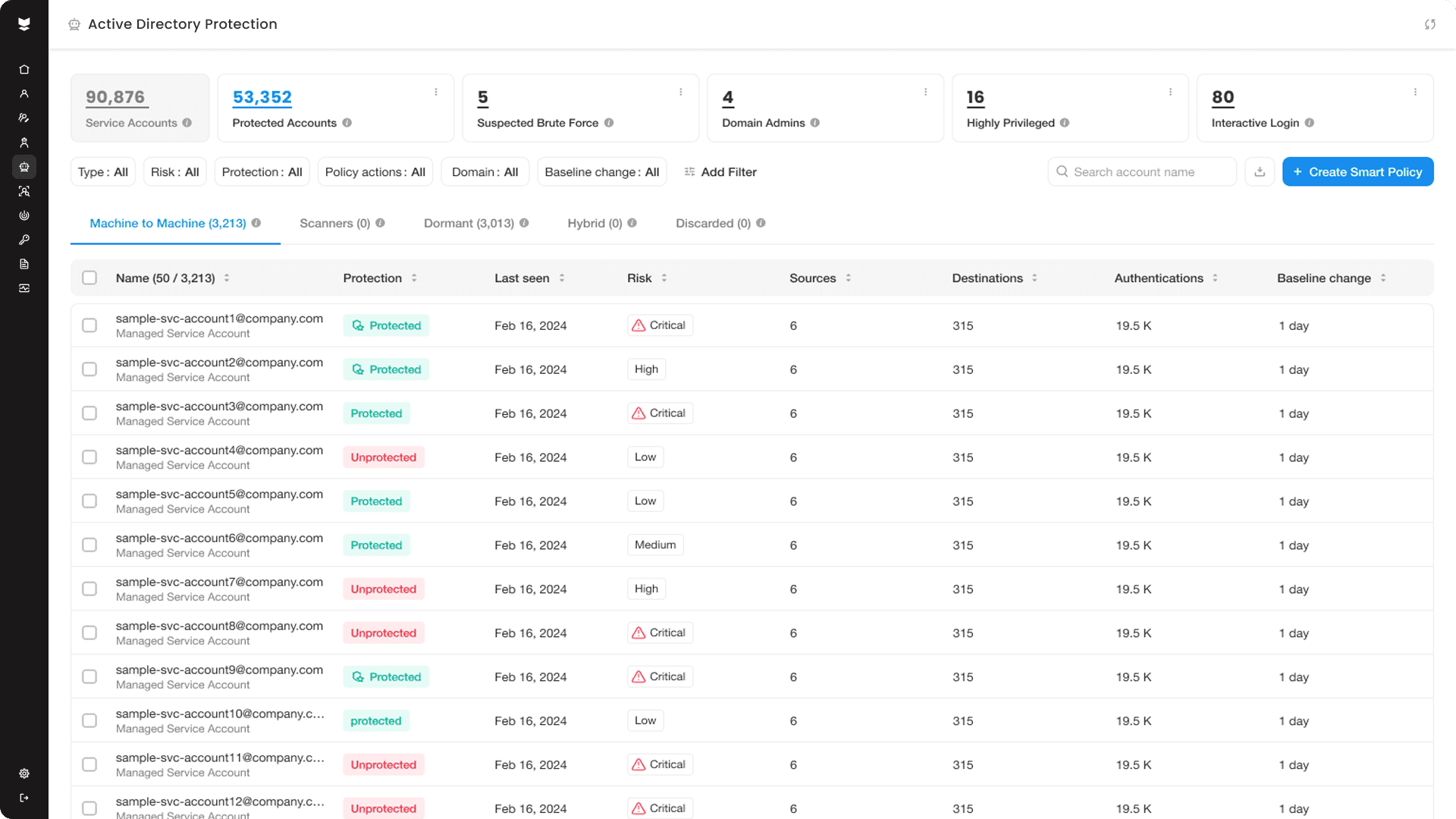
Every identity. Every resource. Detect and block malicious authentications instantly.
Reduce the risk of ransomware and lateral movement
Stop credential misuse and lateral movement at the identity layer with MFA or deny-access policies.
Strengthen compliance readiness
Pass audits and meet compliance frameworks with all the controls, all the visibility, and none of the stress.
Lower costs and accelerate efficiency
Eliminate stale users, shadow admins, and unmanaged service accounts for better AD hygiene and greater operational efficiencies.
Simplify AD security operations
Power up performance and posture by optimizing authentication activity, reducing failed logons, and removing unnecessary NTLM traffic. Modernize AD without re-architecting apps.
Silverfort provided us with a seamless drop-in solution. I'd recommend Silverfort to any organization looking to strengthen their security around admin accounts and service accounts in a minimal disruptive way.
Kurt Gielen
IT Manager
Learn more
FAQs
Does Silverfort replace Active Directory (AD)?
No. It protects AD by enforcing risk-based policies on every authentication attempt.
Can it protect legacy systems that don’t support MFA?
Yes. Silverfort uniquely enforces MFA and access policies on any system that authenticates via AD, without any architectural or code changes.
How quickly can it be deployed?
Typically within hours. Integration with AD is seamless and requires no downtime.